What Is Fedramp and why is it important? FedRAMP, or the Federal Risk and Authorization Management Program, is a government-wide program providing a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services. At WHAT.EDU.VN, we understand that navigating the complexities of cybersecurity compliance can be challenging, and we are here to provide clarity and support. Explore FedRAMP authorization, cloud security, and continuous monitoring, and feel free to ask us any questions you may have!
1. Understanding FedRAMP
1.1. Defining FedRAMP: Securing Cloud Services for the U.S. Government
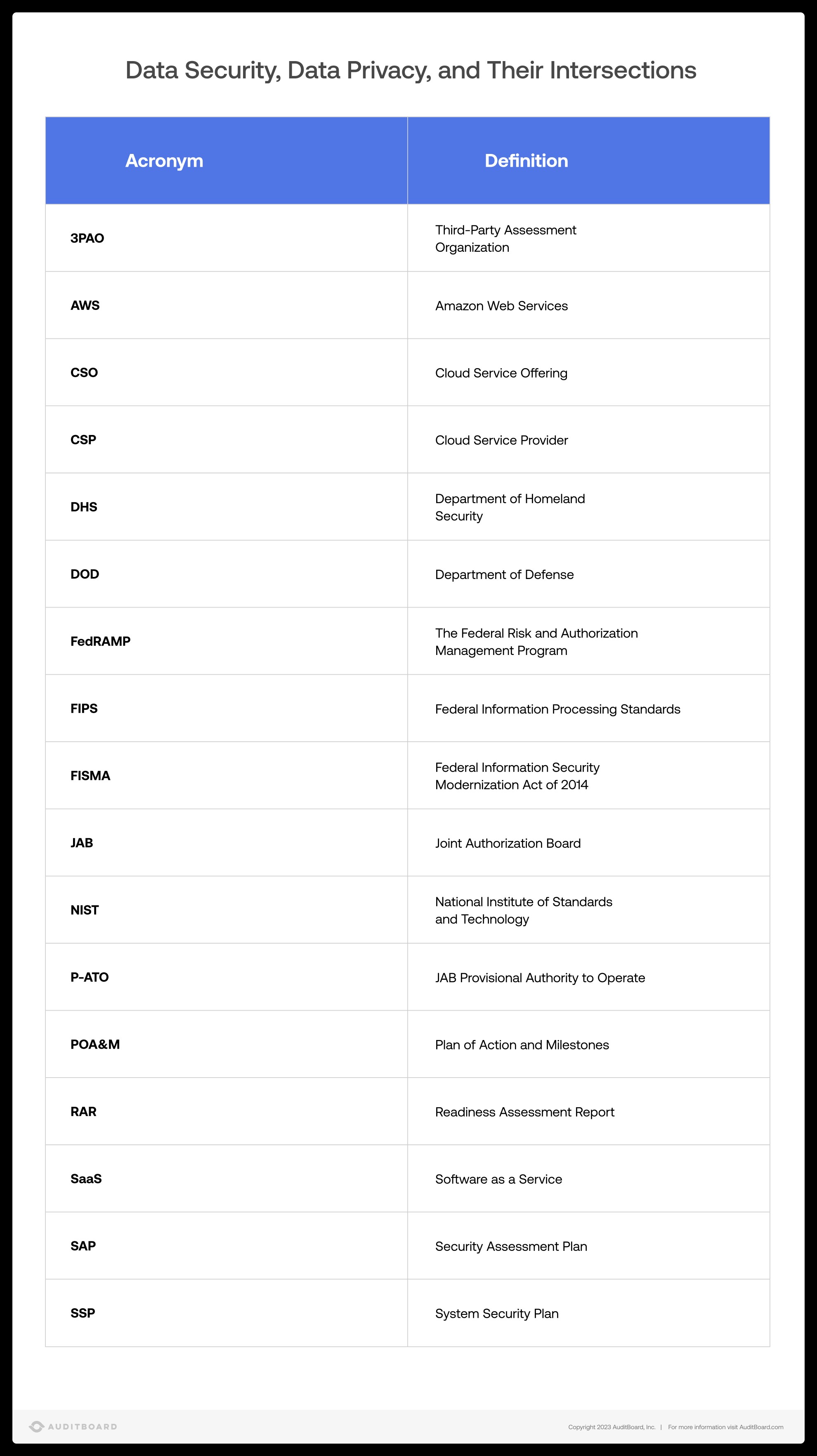
The Federal Risk and Authorization Management Program (FedRAMP) is a U.S. government-wide program that standardizes the approach to security assessment, authorization, and continuous monitoring of cloud products and services. Its core mission is to ensure that cloud service providers (CSPs) offering services to federal agencies meet stringent security requirements, thereby protecting sensitive government data in cloud environments. FedRAMP operates under the guidance of the General Services Administration (GSA) and collaborates with agencies such as the Department of Homeland Security (DHS) and the Department of Defense (DOD).
1.2. The Genesis of FedRAMP: Addressing Cybersecurity Risks in the Cloud
The need for FedRAMP arose from the U.S. Federal Government’s increasing adoption of cloud computing. Policies like Cloud First and Cloud Smart were developed to enhance information sharing and accessibility across federal agencies. However, these initiatives also highlighted the need for robust cybersecurity measures to protect sensitive data in the cloud. FedRAMP was created to address these emerging cyber risks and provide a standardized framework for securing federal data in cloud environments.
1.3. FedRAMP’s Mission: Promoting Secure Cloud Adoption Across the Federal Government
According to the FedRAMP official website, the primary mission of FedRAMP is to accelerate the adoption of secure cloud solutions by federal agencies. This is achieved through a standardized approach to security and risk assessment for cloud technologies. By providing a common framework, FedRAMP aims to reduce redundancy, establish clear security standards, and foster partnerships between cloud providers and the federal government. The program’s goals include expanding the use of secure cloud services, improving the government’s ability to evaluate and authorize cloud solutions, and building strong relationships with FedRAMP stakeholders.
1.4. Key Functions of FedRAMP: PMO and JAB
FedRAMP has two primary functional teams:
- FedRAMP Program Management Office (PMO): The PMO is responsible for the day-to-day operations of the FedRAMP program. It develops and maintains the guidance, templates, and processes for achieving FedRAMP authorization. The PMO also collaborates with government agencies, cloud partners, and third-party assessment organizations (3PAOs).
- Joint Authorization Board (JAB): The JAB serves as the governance and oversight body for FedRAMP. It comprises Chief Information Officers (CIOs) from the DOD, DHS, and GSA. The JAB reviews and approves cloud service offerings (CSOs) for provisional authorization, ensuring they meet the highest security standards.
1.5. Benefits of FedRAMP Compliance: Streamlining Security and Reducing Redundancy
FedRAMP compliance offers several significant benefits for both cloud solutions companies and federal agencies:
- Reduced Redundancy: By establishing a standardized security assessment process, FedRAMP eliminates the need for each agency to conduct its own independent security reviews.
- Established Relationships: FedRAMP fosters collaboration and partnerships between cloud providers and the federal government.
- Transparent Standards: FedRAMP provides clear and transparent security standards, making it easier for CSPs to understand and meet the government’s requirements.
- Government-Wide Security Authorizations: FedRAMP authorizations are recognized across the federal government, allowing agencies to quickly adopt secure cloud solutions.
1.6. FedRAMP MarketPlace: A Repository of Authorized Cloud Service Offerings
The FedRAMP MarketPlace is a valuable resource for federal agencies and CSPs alike. It is a repository of authorized Cloud Service Offerings (CSOs) and related documentation. Through the MarketPlace, users can find CSOs with FedRAMP designations, identify federal agencies using specific CSOs, and locate 3PAOs qualified to perform FedRAMP assessments.
2. Understanding FedRAMP Compliance
2.1. Defining FedRAMP Compliance: Meeting Stringent Security Standards
FedRAMP compliance signifies that a Cloud Service Provider (CSP) has met the rigorous security standards established by the Federal Risk and Authorization Management Program (FedRAMP). This means the CSP’s Cloud Service Offering (CSO) has undergone a thorough assessment and authorization process, ensuring it can securely handle sensitive government data.
2.2. Who Needs FedRAMP Compliance? Cloud Service Providers Serving Federal Agencies
Any Cloud Service Provider (CSP) that intends to provide a Cloud Service Offering (CSO) to a federal agency must achieve FedRAMP authorization. This requirement applies to all types of cloud services, including Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS).
2.3. The Importance of Continuous Monitoring: Maintaining Ongoing Security Posture
Achieving FedRAMP authorization is not a one-time event. CSPs must continuously monitor their systems and maintain their security posture to remain compliant. This includes regular vulnerability scanning, penetration testing, and security assessments.
2.4. The Two Pathways to FedRAMP Authorization: Agency and JAB Processes
There are two primary pathways to achieving FedRAMP authorization:
- Agency Authorization: In this process, a CSP works directly with a specific federal agency to obtain an Authority to Operate (ATO).
- Joint Authorization Board (JAB) Authorization: The JAB, consisting of CIOs from the DOD, DHS, and GSA, grants a Provisional Authority to Operate (P-ATO) to CSOs that meet its stringent security requirements.
2.5. FedRAMP Compliance and NIST 800-53: Aligning with Federal Security Guidelines
FedRAMP compliance is closely aligned with the National Institute of Standards and Technology (NIST) Special Publication 800-53, which provides a catalog of security and privacy controls for federal information systems and organizations. FedRAMP leverages these controls to establish a baseline of security requirements for cloud services.
2.6. When is FedRAMP Required?
FedRAMP is required whenever a federal agency uses a cloud service to store or process sensitive federal data. This ensures that all cloud services used by the government meet a minimum level of security.
2.7. Benefits of FedRAMP Authorization:
- Access to the Federal Market: FedRAMP authorization allows CSPs to offer their services to federal agencies, opening up a significant market opportunity.
- Enhanced Security Posture: The FedRAMP compliance process helps CSPs strengthen their security controls and improve their overall security posture.
- Competitive Advantage: FedRAMP authorization demonstrates a CSP’s commitment to security and can provide a competitive advantage in the marketplace.
Source: FedRAMP Authorization Process
3. FedRAMP Compliance Requirements
3.1. Overview of FedRAMP Compliance Requirements: A Step-by-Step Approach
Achieving FedRAMP compliance involves a structured process that includes assessment, authorization, and continuous monitoring. Here’s a breakdown of the key steps:
3.2. Step 1: Compile Initial FedRAMP Documents: Leveraging Available Resources
The first step in the FedRAMP authorization process is to gather and familiarize yourself with the necessary documentation. The FedRAMP website offers a wealth of resources, including templates and guides, to help you prepare for the authorization process.
3.3. Step 2: FIPS 199 Assessment: Categorizing Data Impact Levels
FIPS 199, the Federal Information Processing Standard, is used to categorize the data stored and transmitted by cloud computing services based on their potential impact. Data is classified as low, moderate, or high-impact, which determines the stringency of the security controls a CSP must implement.
3.4. Step 3: Conduct 3PAO Readiness Assessment: Evaluating Security Posture
A 3PAO (Third-Party Assessment Organization) conducts a readiness assessment to evaluate a CSP’s security posture and identify any gaps in compliance. This step is mandatory for the JAB authorization path and highly recommended for the Agency Authorization path.
3.5. Step 4: Create a Plan of Action and Milestones (POA&M) and Execute: Addressing Security Gaps
The POA&M is a document that outlines the steps a CSP will take to address any identified security gaps. It includes a timeline for remediation and assigns responsibility for each task.
3.6. Step 5: Follow the Agency or JAB Process for Authorization: Obtaining ATO or P-ATO
The next step is to follow either the Agency Process or the JAB Process to obtain authorization. The Agency Process involves working directly with a federal agency, while the JAB Process involves working with the Joint Authorization Board.
3.7. Step 6: Maintain Continuous Monitoring: Ensuring Ongoing Security Compliance
Once an organization has received formal authorization in the form of an ATO or P-ATO, they are then subject to continuous monitoring, both internally and by the federal agencies they work with. To stay FedRAMP compliant, organizations may have to provide evidence that certain key controls are operating on a monthly and/or annual basis, such as through vulnerability scanning and penetration testing.
3.8. Documents and Templates:
- System Security Plan (SSP)
- Security Assessment Report (SAR)
- Plan of Action and Milestones (POA&M)
- Readiness Assessment Report (RAR)
4. Navigating the Different Paths to FedRAMP Compliance
4.1. Understanding the Two Paths to FedRAMP Authorization: Agency vs. JAB
There are two distinct paths to achieving FedRAMP compliance: the Agency Authorization path and the Joint Authorization Board (JAB) Authorization path. The choice between these paths depends on the CSP’s relationship with federal agencies and the nature of the cloud service offering.
4.2. Agency Authorization: Partnering Directly with a Federal Agency
The Agency Authorization path involves a CSP working directly with a specific federal agency to obtain an Authority to Operate (ATO). This path is suitable for CSPs that have an existing relationship with an agency or are developing a cloud service specifically tailored to that agency’s needs.
4.3. JAB Authorization: Seeking Government-Wide Approval
The JAB Authorization path involves a CSP seeking a Provisional Authority to Operate (P-ATO) from the Joint Authorization Board (JAB). The JAB comprises CIOs from the DOD, DHS, and GSA. This path is ideal for CSPs that want to offer their cloud services to multiple federal agencies and seek a government-wide authorization.
4.4. Key Differences Between Agency and JAB Authorization:
- Partnering Agency: Agency Authorization involves working with a specific federal agency, while JAB Authorization involves working with the Joint Authorization Board.
- Authorization Scope: Agency Authorization results in an ATO that is specific to the partnering agency, while JAB Authorization results in a P-ATO that can be leveraged by multiple agencies.
- Readiness Assessment: A 3PAO Readiness Assessment is optional for Agency Authorization but mandatory for JAB Authorization.
- Authorization Timeline: Agency Authorization may have a shorter timeline than JAB Authorization, as it involves a single agency.
4.5. Choosing the Right Path: Factors to Consider
When deciding between the Agency and JAB Authorization paths, CSPs should consider the following factors:
- Existing Relationships: Does the CSP have an existing relationship with a federal agency?
- Target Market: Does the CSP want to offer its services to a single agency or multiple agencies?
- Authorization Timeline: How quickly does the CSP need to achieve authorization?
- Resources: Does the CSP have the resources to meet the requirements of each path?
4.6. GSA Flow Charts:
GSA provides useful flow charts for both JAB and Agency authorization to illustrate the different processes.
5. Understanding the Categories of FedRAMP Compliance
5.1. Defining Risk Impact Levels: Categorizing Data Sensitivity
FedRAMP categorizes cloud service offerings (CSOs) into three risk impact levels: low, moderate, and high. These levels are based on the potential impact of a security breach on the confidentiality, integrity, and availability of data. The risk level determines the number and stringency of security controls required for FedRAMP compliance.
5.2. Low Impact: Limited Adverse Effects
A low-impact CSO is one where the loss of confidentiality, integrity, or availability would result in limited adverse effects on an agency’s operations, assets, or individuals. Examples of low-impact data include public information and websites.
5.3. Moderate Impact: Serious Adverse Effects
A moderate-impact CSO is one where the loss of confidentiality, integrity, or availability would result in serious adverse effects on an agency’s operations, assets, or individuals. These effects could include financial losses or harm to individuals, but not loss of life or physical damage. Most organizations fall into this category.
5.4. High Impact: Severe or Catastrophic Effects
A high-impact CSO is one where the loss of confidentiality, integrity, or availability would result in severe or catastrophic effects on an agency’s operations, assets, or individuals. This category typically includes data related to law enforcement, emergency services, financial systems, or health systems.
5.5. Impact Levels and Security Controls: A Direct Correlation
The higher the impact level, the more stringent the security controls required for FedRAMP compliance. High-impact CSOs require the most comprehensive and rigorous security measures.
5.6. Examples of Data Types by Impact Level:
- Low Impact: Public websites, brochures, public information
- Moderate Impact: Personally Identifiable Information (PII), financial records, email
- High Impact: Law enforcement data, emergency services data, health records
6. Achieving FedRAMP Certification: A Detailed Overview
6.1. The Path to FedRAMP Certification: A Comprehensive Process
Achieving FedRAMP certification is a rigorous and demanding process, especially for CSPs categorized as high-risk impact. However, it is a worthwhile investment that opens doors to lucrative partnerships with federal agencies.
6.2. Cost Considerations: Budgeting for FedRAMP Compliance
FedRAMP compliance can be expensive, requiring collaboration across the organization. Costs include the initial assessment, remediation of any identified security gaps, and ongoing continuous monitoring activities.
6.3. Collaboration with a 3PAO: Ensuring Objective Assessment
FedRAMP requires CSPs to partner with a 3PAO for Full Security Assessments. This ensures an objective and independent evaluation of the CSP’s security posture.
6.4. Continuous Monitoring: Maintaining Ongoing Compliance
Continuous monitoring is an essential aspect of FedRAMP compliance. CSPs must continuously monitor their systems and provide evidence that key controls are operating effectively.
6.5. FedRAMP Marketplace: Showcasing Authorized Cloud Service Offerings
Once a CSP achieves FedRAMP authorization, it can be listed in the FedRAMP Marketplace. This allows federal agencies to easily identify and partner with authorized cloud providers.
6.6. Steps to achieve FedRAMP certification:
- Compile Initial FedRAMP Documents
- FIPS 199 Assessment
- Conduct 3PAO Readiness Assessment
- Create a Plan of Action and Milestones (POA&M) and Execute
- Follow the Agency or JAB Process for Authorization
- Maintain Continuous Monitoring
6.7. Continuous Monitoring Requirements:
- Vulnerability scanning
- Penetration testing
- Security assessments
- Incident response
7. Key Takeaways and Conclusion
7.1. FedRAMP Compliance: A Challenging but Rewarding Endeavor
FedRAMP compliance can be a challenging process, but it is essential for CSPs seeking to work with federal agencies. By understanding the requirements and following a structured approach, CSPs can successfully navigate the FedRAMP process and achieve authorization.
7.2. Compliance Management Software: Streamlining the FedRAMP Process
Compliance management software can help CSPs streamline the FedRAMP process by automating tasks, tracking progress, and managing documentation.
7.3. Staying Up-to-Date: Keeping Pace with Evolving Requirements
FedRAMP requirements are constantly evolving, so it is important for CSPs to stay up-to-date on the latest guidance and best practices.
7.4. FedRAMP Compliance Takeaways:
- FedRAMP compliance is essential for CSPs seeking to work with federal agencies.
- The FedRAMP process involves assessment, authorization, and continuous monitoring.
- There are two paths to FedRAMP authorization: Agency and JAB.
- FedRAMP categorizes CSOs into three risk impact levels: low, moderate, and high.
- Continuous monitoring is an essential aspect of FedRAMP compliance.
- Compliance management software can help streamline the FedRAMP process.
7.5. Still Have Questions?
We understand that navigating the complexities of FedRAMP can be daunting. At WHAT.EDU.VN, we are committed to providing you with the information and support you need to succeed. If you have any questions about FedRAMP compliance or other cybersecurity topics, please don’t hesitate to reach out. Our team of experts is here to help you every step of the way.
8. Frequently Asked Questions About FedRAMP Compliance
8.1. What Is FedRAMP?
The Federal Risk and Authorization Management Program (FedRAMP) is a government-wide program that promotes the adoption of secure cloud services across the federal government by providing a standardized approach to security and risk assessment for cloud technologies and federal agents.
8.2. What Does It Mean to Be FedRAMP Compliant?
To be FedRAMP compliant, an organization must establish strong internal controls over their Cloud Service Offering (CSO) in compliance with FedRAMP requirements.
8.3. What Are FedRAMP Compliance Requirements?
FedRAMP compliance requirements differ based on whether the CSO is classified as high, moderate, or low impact, but generally pull from the NIST 800-53 guidelines.
8.4. What Are the Different Paths to Achieve FedRAMP Compliance?
There are two different paths to achieve FedRAMP compliance: Agency, which results in an Authorization to Operate (ATO) and JAB, which results in a Provisional Authorization to Operate (P-ATO).
8.5. What is a 3PAO?
A Third-Party Assessment Organization (3PAO) is an independent organization that is accredited by FedRAMP to assess cloud service offerings (CSOs) for compliance with FedRAMP requirements.
8.6. What is a System Security Plan (SSP)?
A System Security Plan (SSP) is a document that describes the security controls that are in place to protect a cloud service offering (CSO). The SSP is a key component of the FedRAMP authorization process.
8.7. What is a Security Assessment Report (SAR)?
A Security Assessment Report (SAR) is a report that documents the findings of a security assessment of a cloud service offering (CSO). The SAR is prepared by a 3PAO and is used to determine whether the CSO meets FedRAMP requirements.
8.8. What is a Plan of Action and Milestones (POA&M)?
A Plan of Action and Milestones (POA&M) is a document that outlines the steps that will be taken to address any security weaknesses that are identified during a security assessment. The POA&M includes a timeline for completing each milestone.
8.9. How long does it take to achieve FedRAMP authorization?
The time it takes to achieve FedRAMP authorization can vary depending on the complexity of the cloud service offering (CSO) and the chosen authorization path (Agency or JAB). However, it typically takes several months to a year to complete the process.
8.10. How much does it cost to achieve FedRAMP authorization?
The cost of achieving FedRAMP authorization can vary depending on the size and complexity of the cloud service offering (CSO). However, it typically costs hundreds of thousands of dollars to complete the process.
Do you have more questions about FedRAMP or need assistance with navigating the compliance process? Don’t hesitate to ask your questions on WHAT.EDU.VN! We’re here to provide clear, accurate, and helpful answers to all your inquiries, free of charge.
Address: 888 Question City Plaza, Seattle, WA 98101, United States
WhatsApp: +1 (206) 555-7890
Website: what.edu.vn