Phishing is a deceptive cyberattack where malicious actors impersonate trusted entities via email, phone, or text to trick individuals into revealing sensitive information. At WHAT.EDU.VN, we’re dedicated to educating you about online safety and providing resources to safeguard against digital threats. Learn about phishing scams, email security, and ways to protect your personal data.
1. What Is Phishing and How Does It Work?
Phishing is a type of online fraud where attackers attempt to steal sensitive information such as usernames, passwords, credit card details, and personal identification numbers (PINs). They often disguise themselves as legitimate organizations or people to gain your trust.
1.1. Definition of Phishing
Phishing is defined as a cybercrime where individuals are contacted via email, telephone, or text message by someone posing as a legitimate institution to lure them into providing sensitive data. This data is then used to access important accounts and can result in identity theft and financial loss. It’s essential to stay informed about cyber security and protect your data.
1.2. How Phishing Attacks Work
Phishing attacks typically involve the following steps:
- Impersonation: Attackers create emails, websites, or messages that mimic trusted organizations such as banks, social media platforms, or government agencies.
- Deception: The messages often contain urgent or enticing content designed to provoke a quick response. They might claim your account has been compromised, you’ve won a prize, or there’s an urgent issue requiring immediate action.
- Data Theft: Victims are directed to fake websites or asked to provide sensitive information directly. Once the information is entered, it is harvested by the attackers.
1.3. Real-World Examples of Phishing Attacks
- Email Phishing: Receiving an email claiming to be from your bank asking you to update your account information.
- Spear Phishing: A targeted attack against specific individuals, such as employees within a company, using personalized information to increase credibility.
- Whaling: Phishing attacks directed at high-profile targets, such as CEOs or senior executives.
- Smishing (SMS Phishing): Receiving a text message claiming you have a package waiting for delivery and asking for payment to release it.
- Vishing (Voice Phishing): Receiving a phone call from someone claiming to be from the IRS, threatening legal action if you don’t pay immediately.
2. Common Types of Phishing Attacks
Understanding the different types of phishing attacks can help you recognize and avoid them. Here are some common types:
| Type | Description | Example |
|---|---|---|
| Email Phishing | Attackers send deceptive emails to a broad audience, hoping to trick recipients into revealing sensitive information. | An email claiming to be from PayPal asking you to verify your account details. |
| Spear Phishing | A targeted attack that focuses on specific individuals, often using personalized information to increase credibility. | An email to an employee referencing internal projects or colleagues to trick them into clicking a malicious link. |
| Whaling | Phishing attacks directed at high-profile targets, such as CEOs or senior executives. | An email to a CEO appearing to be from a trusted business partner requesting urgent financial information. |
| Smishing | Phishing attacks conducted via SMS or text messages. | A text message claiming you’ve won a prize and asking you to click a link to claim it. |
| Vishing | Phishing attacks carried out over the phone, often using social engineering tactics to manipulate victims. | A phone call from someone claiming to be from tech support asking for remote access to your computer to fix a problem. |
| Pharming | Redirects users to fraudulent websites without their knowledge or consent, even if they type the correct URL. | Users attempting to access their bank’s website are unknowingly redirected to a fake site. |
| Angler Phishing | Uses social media to target users. Attackers pose as customer service representatives to trick users. | A fake customer service account on Twitter asking for personal details to resolve a supposed issue. |
2.1. Email Phishing
Email phishing is one of the most common types of phishing attacks. Attackers send deceptive emails that appear to be from legitimate organizations to trick recipients into revealing sensitive information.
2.1.1. How to Identify Email Phishing
- Check the Sender’s Address: Verify the email address to ensure it matches the sender’s claimed identity. Look for misspellings or unusual domain names.
- Examine the Subject Line: Be wary of subject lines that create a sense of urgency or promise something too good to be true.
- Review the Content: Look for grammatical errors, spelling mistakes, and unprofessional language.
- Hover Over Links: Hover over links to see the actual URL. If it doesn’t match the claimed destination, it’s likely a phishing attempt.
- Don’t Open Suspicious Attachments: Avoid opening attachments from unknown senders, as they may contain malware.
2.2. Spear Phishing
Spear phishing is a targeted type of phishing attack that focuses on specific individuals or organizations. Attackers gather information about their targets to craft personalized and convincing emails.
2.2.1. Why Spear Phishing Is More Effective
Spear phishing is more effective because it leverages personalized information to gain the victim’s trust. Attackers may use details about the target’s job, colleagues, or personal interests to make the email appear legitimate.
2.2.2. Protection Against Spear Phishing
- Verify Requests: Always verify requests for sensitive information through a separate communication channel, such as a phone call.
- Be Suspicious of Unsolicited Emails: Be cautious of unsolicited emails, especially those asking for personal details or financial information.
- Educate Employees: Train employees to recognize and report spear phishing attempts.
2.3. Whaling
Whaling is a type of phishing attack that targets high-profile individuals, such as CEOs, CFOs, and other senior executives. These attacks aim to steal sensitive information or gain access to valuable company assets.
2.3.1. The Risks of Whaling Attacks
Whaling attacks can lead to significant financial losses, reputational damage, and data breaches. Executives often have access to critical systems and data, making them attractive targets for cybercriminals.
2.3.2. How to Protect Executives from Whaling
- Implement Strong Security Measures: Enforce multi-factor authentication, use strong passwords, and regularly update security software.
- Provide Executive Training: Offer specialized training to executives on how to identify and respond to whaling attacks.
- Monitor Email Traffic: Use advanced email security solutions to detect and block suspicious emails targeting executives.
2.4. Smishing (SMS Phishing)
Smishing is a type of phishing attack that uses SMS or text messages to trick victims into revealing sensitive information or downloading malware.
2.4.1. Recognizing Smishing Attempts
- Unsolicited Messages: Be wary of unsolicited text messages from unknown senders.
- Urgent Requests: Watch out for messages that create a sense of urgency or demand immediate action.
- Suspicious Links: Avoid clicking on links in text messages from unknown sources.
2.4.2. Best Practices for Smishing Prevention
- Don’t Trust Unknown Numbers: Be skeptical of text messages from numbers you don’t recognize.
- Verify Information: If a message claims to be from a legitimate organization, contact them directly to verify the information.
- Report Suspicious Messages: Report smishing attempts to your mobile carrier and relevant authorities.
2.5. Vishing (Voice Phishing)
Vishing is a type of phishing attack that uses phone calls to deceive victims into providing sensitive information. Attackers often impersonate trusted organizations or individuals to gain the victim’s trust.
2.5.1. Common Vishing Scenarios
- Tech Support Scams: Callers claim to be from tech support and ask for remote access to your computer to fix a problem.
- IRS Scams: Callers impersonate IRS agents and threaten legal action if you don’t pay immediately.
- Lottery Scams: Callers claim you’ve won a lottery and ask for personal information to claim your prize.
2.5.2. Staying Safe from Vishing
- Be Suspicious of Unsolicited Calls: Be cautious of unsolicited phone calls asking for personal or financial information.
- Verify the Caller’s Identity: If you receive a call from someone claiming to be from a legitimate organization, verify their identity by contacting the organization directly.
- Never Share Sensitive Information: Never share sensitive information over the phone with someone you don’t trust.
2.6. Pharming
Pharming is a type of cyberattack that redirects users to fraudulent websites without their knowledge or consent. Unlike phishing, pharming doesn’t require the victim to click on a malicious link.
2.6.1. How Pharming Works
Pharming involves manipulating DNS (Domain Name System) settings to redirect users to fake websites, even if they type the correct URL. This can be done by compromising a DNS server or by infecting a user’s computer with malware.
2.6.2. Protecting Against Pharming Attacks
- Use a Reputable DNS Provider: Choose a DNS provider with strong security measures to protect against DNS manipulation.
- Keep Your Software Updated: Regularly update your operating system, browser, and antivirus software to protect against malware infections.
- Be Wary of Suspicious Websites: Avoid visiting websites with poor security or suspicious content.
2.7. Angler Phishing
Angler phishing is a type of phishing attack that uses social media to target users. Attackers pose as customer service representatives or other trusted entities to trick users into revealing sensitive information.
2.7.1. How Angler Phishing Operates
Attackers monitor social media platforms for users who are complaining about a company or service. They then pose as customer service representatives and offer to help, often asking for personal details to resolve the issue.
2.7.2. Tips to Avoid Angler Phishing
- Verify the Account: Check the account’s authenticity by looking for verified badges or official contact information.
- Be Cautious of Unsolicited Help: Be wary of unsolicited offers of help from unknown accounts.
- Contact the Company Directly: If you need customer service, contact the company directly through their official website or phone number.
3. Common Features of Phishing Emails
Recognizing the common characteristics of phishing emails can help you identify and avoid these scams. Here are some typical features to watch out for:
3.1. Too Good To Be True
Phishing emails often contain offers or promises that seem too good to be true. These could include claims that you’ve won a lottery, received a large inheritance, or are eligible for a valuable prize.
3.1.1. Examples of Overly Lucrative Offers
- “You’ve won a free iPhone!”
- “Claim your prize of $1,000,000!”
- “Get a free vacation to the Bahamas!”
3.1.2. Staying Grounded in Reality
Remember, if something seems too good to be true, it probably is. Legitimate organizations rarely offer extravagant prizes or giveaways through unsolicited emails. Always be skeptical of such offers.
3.2. Sense of Urgency
Phishing emails frequently create a sense of urgency to pressure you into acting quickly without thinking. They might claim that your account will be suspended if you don’t update your information immediately or that a special offer is only available for a limited time.
3.2.1. How Attackers Use Urgency
Attackers use urgency to bypass your critical thinking. When you feel pressured to act quickly, you’re more likely to make mistakes and overlook red flags.
3.2.2. Responding Calmly
Take a deep breath and resist the urge to act immediately. Legitimate organizations will give you ample time to respond and will never pressure you to provide sensitive information through email.
3.3. Hyperlinks
Hyperlinks in phishing emails can be deceptive. The displayed text may appear to link to a legitimate website, but the actual URL could be different.
3.3.1. Checking Link Destinations
Hover your mouse over the link (without clicking) to see the actual URL. If the URL doesn’t match the claimed destination or contains misspellings, it’s likely a phishing attempt. For example, www.bankofarnerica.com is a common phishing trick, where the ‘m’ is replaced with ‘rn’.
3.3.2. Safe Browsing Habits
Always type the URL directly into your browser instead of clicking on links in emails. This ensures you’re visiting the legitimate website.
3.4. Attachments
Attachments in phishing emails can contain malware or other malicious software. Avoid opening attachments from unknown senders, as they could infect your computer.
3.4.1. Risky File Types
Be particularly cautious of file types such as .exe, .zip, .scr, and .docm, as these are commonly used to distribute malware.
3.4.2. Secure Attachment Handling
The only file type that is generally safe to click on is a .txt file. If you receive an attachment you weren’t expecting or that doesn’t make sense, don’t open it.
3.5. Unusual Sender
If an email seems out of the ordinary, unexpected, or suspicious in any way, don’t click on it. This could include emails from unknown senders, emails that don’t match the sender’s typical communication style, or emails that contain unusual requests.
3.5.1. Recognizing Impostors
Attackers often impersonate trusted individuals or organizations to trick you into revealing sensitive information. Always verify the sender’s identity before responding to an email.
3.5.2. Trust Your Gut
If something feels off about an email, trust your intuition. It’s better to be cautious than to fall victim to a phishing scam.
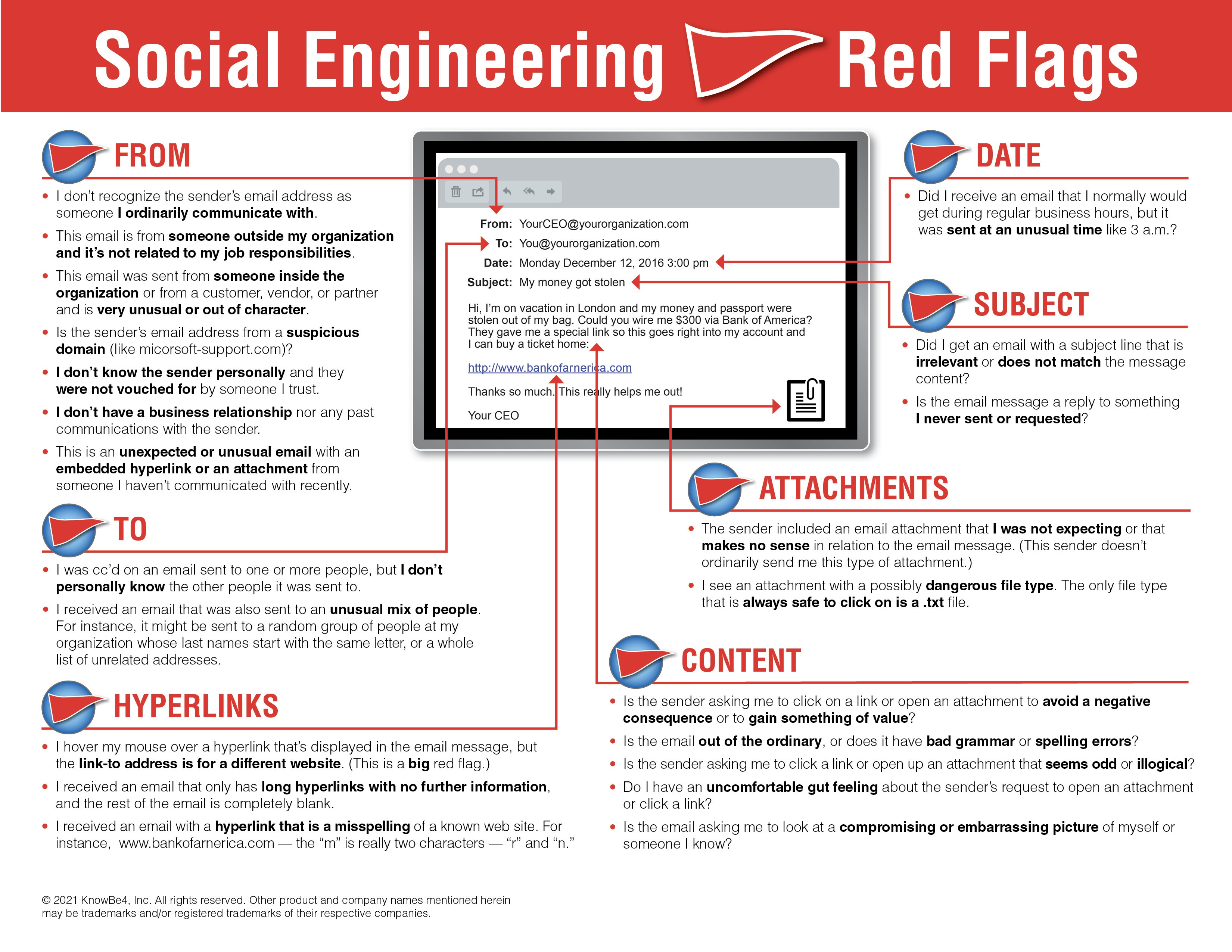 Social Engineering Red Flags Commonly Seen in Phishing Emails
Social Engineering Red Flags Commonly Seen in Phishing Emails
4. Preventing Phishing Attacks
Protecting yourself from phishing attacks requires a combination of awareness, caution, and proactive security measures. Here are some steps you can take to prevent phishing:
4.1. Use Spam Filters
Spam filters can help block phishing emails from reaching your inbox. These filters analyze the content, origin, and structure of emails to identify and block spam.
4.1.1. How Spam Filters Work
Spam filters use various techniques to identify spam, including:
- Content Analysis: Examining the content of the email for keywords and phrases commonly used in spam.
- Sender Reputation: Checking the sender’s IP address and domain against blacklists of known spam sources.
- Heuristic Analysis: Analyzing the structure and formatting of the email for suspicious patterns.
4.1.2. Limitations of Spam Filters
Spam filters are not always 100% accurate and may occasionally block legitimate emails. It’s important to regularly check your spam folder to ensure you’re not missing any important messages.
4.2. Adjust Browser Settings
Adjust your browser settings to prevent fraudulent websites from opening. Browsers keep a list of fake websites and will block access or display an alert message if you try to visit one of these sites.
4.2.1. Enabling Security Features
Enable security features such as:
- Phishing Protection: This feature warns you when you visit a website that has been identified as a phishing site.
- Safe Browsing: This feature blocks access to websites known to distribute malware or engage in other malicious activities.
4.2.2. Keeping Your Browser Updated
Regularly update your browser to ensure you have the latest security patches and features.
4.3. Change Passwords Regularly
Change your passwords regularly and never use the same password for multiple accounts. This helps protect your accounts in case one of your passwords is compromised.
4.3.1. Creating Strong Passwords
Use strong, unique passwords that are at least 12 characters long and include a combination of uppercase and lowercase letters, numbers, and symbols.
4.3.2. Using Password Managers
Consider using a password manager to securely store and manage your passwords. Password managers can also generate strong, unique passwords for each of your accounts.
4.4. Report Phishing
Report phishing attempts to industry groups and relevant authorities. This helps them take action against fraudulent websites and protect others from falling victim to phishing scams.
4.4.1. Reporting to Industry Groups
Many industry groups, such as the Anti-Phishing Working Group (APWG), collect and analyze phishing reports to combat phishing attacks.
4.4.2. Reporting to Authorities
You can also report phishing attempts to law enforcement agencies, such as the Federal Trade Commission (FTC) in the United States.
4.5. Security Awareness Training
Organizations should provide security awareness training to employees to help them recognize and avoid phishing attacks. Training should cover topics such as:
4.5.1. Recognizing Phishing Emails
Teaching employees how to identify the common characteristics of phishing emails, such as suspicious sender addresses, urgent requests, and grammatical errors.
4.5.2. Safe Browsing Practices
Educating employees on safe browsing practices, such as avoiding suspicious websites and verifying the authenticity of links.
4.5.3. Password Security
Providing guidance on creating strong passwords and using password managers.
4.6. Changes in Browsing Habits
Make changes to your browsing habits to prevent phishing attacks. This includes:
4.6.1. Verifying Information
If an email or website requires verification, always contact the company personally before entering any details online.
4.6.2. Hovering Over URLs
If there is a link in an email, hover over the URL first to see the actual destination. Secure websites with a valid Secure Socket Layer (SSL) certificate begin with “https”.
Generally, emails sent by cybercriminals are masked so they appear to be sent by a business whose services are used by the recipient. A bank will not ask for personal information via email or suspend your account if you do not update your personal details within a certain period of time. Most banks and financial institutions also usually provide an account number or other personal details within the email, which ensures it’s coming from a reliable source.
5. Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
6. FAQ About Phishing
| Question | Answer |
|---|---|
| What Is Phishing? | Phishing is a cybercrime where attackers attempt to steal sensitive information by impersonating trusted entities. |
| How can I identify a phishing email? | Look for suspicious sender addresses, urgent requests, grammatical errors, and links that don’t match the claimed destination. |
| What should I do if I receive a phishing email? | Don’t click on any links or open any attachments. Report the email to your email provider and relevant authorities. |
| How can I protect myself from phishing attacks? | Use spam filters, adjust browser settings, change passwords regularly, and stay informed about the latest phishing techniques. |
| What is spear phishing? | Spear phishing is a targeted type of phishing attack that focuses on specific individuals or organizations. |
| What is whaling? | Whaling is a type of phishing attack that targets high-profile individuals, such as CEOs or senior executives. |
| What is smishing? | Smishing is a type of phishing attack that uses SMS or text messages to trick victims into revealing sensitive information. |
| What is vishing? | Vishing is a type of phishing attack that uses phone calls to deceive victims into providing sensitive information. |
| What is pharming? | Pharming is a type of cyberattack that redirects users to fraudulent websites without their knowledge or consent. |
| What is angler phishing? | Angler phishing is a type of phishing attack that uses social media to target users by posing as customer service representatives. |
| How can security awareness training help prevent phishing attacks? | Security awareness training educates employees on how to recognize and avoid phishing attacks, reducing the risk of successful phishing attempts. |
| Why is it important to report phishing attempts? | Reporting phishing attempts helps industry groups and authorities take action against fraudulent websites and protect others from falling victim to phishing scams. |
| What are the key features of a strong password? | A strong password should be at least 12 characters long and include a combination of uppercase and lowercase letters, numbers, and symbols. |
| How often should I change my passwords? | It’s recommended to change your passwords every 3 to 6 months to maintain a high level of security. |
| What should I do if I think my account has been compromised by phishing? | Change your password immediately, monitor your account for suspicious activity, and notify your bank or other relevant organizations. |
7. Need More Answers? Ask WHAT.EDU.VN!
Do you have questions about phishing or any other topic? At WHAT.EDU.VN, we provide a free platform for you to ask any question and receive quick, accurate answers from a community of knowledgeable individuals.
7.1. Why Choose WHAT.EDU.VN?
- Free Service: Ask any question without incurring any costs.
- Quick Answers: Get responses to your questions quickly and efficiently.
- Knowledgeable Community: Connect with experts and enthusiasts who can provide valuable insights.
- Easy to Use: Our platform is user-friendly and accessible to everyone.
7.2. How to Ask a Question on WHAT.EDU.VN
- Visit our website at WHAT.EDU.VN.
- Create a free account or log in if you already have one.
- Type your question into the search bar or submission form.
- Provide any relevant details or context.
- Submit your question and wait for responses from our community.
7.3. Contact Us
For any inquiries or assistance, feel free to reach out to us:
- Address: 888 Question City Plaza, Seattle, WA 98101, United States
- WhatsApp: +1 (206) 555-7890
- Website: WHAT.EDU.VN
At what.edu.vn, we are committed to providing a safe and informative platform for everyone to ask questions and receive answers. Don’t hesitate to reach out with any questions you may have!