What Is Pinging? It’s a fundamental network diagnostic tool, and at WHAT.EDU.VN, we’ll break down what it means, how it works, and why it’s important. Discover the power of pinging and troubleshoot your network with ease. Explore network latency, round-trip time, and ICMP protocol today.
1. Introduction: Unveiling the Power of Pinging
Pinging is a cornerstone of network troubleshooting, a simple yet powerful tool that allows you to check the reachability of a device on a network. Think of it as a digital “echo” – you send out a signal, and if the target device is active and connected, it sends a signal back. At WHAT.EDU.VN, we understand the importance of accessible information, and we’re here to guide you through the world of pinging, regardless of your technical background. Whether you’re a student grappling with networking concepts, a professional troubleshooting network issues, or simply a curious individual, this comprehensive guide will equip you with the knowledge you need to understand and utilize pinging effectively. Join us as we delve into the mechanics, applications, and nuances of this essential network tool. Need answers quickly? Ask your questions for free on WHAT.EDU.VN!
2. Demystifying the Ping Command: What Does It Really Do?
At its core, pinging is a command-line utility used to test the reachability of a host on an Internet Protocol (IP) network. But what does that actually mean? Let’s break it down:
- Reachability: This refers to whether or not your computer can successfully communicate with another device on the network, such as a website server, another computer, or a network printer.
- IP Network: The Internet and most local networks rely on the IP protocol to transmit data. Each device on the network has a unique IP address, similar to a postal address, that allows data to be routed correctly.
- Command-Line Utility: Ping is typically accessed through a command-line interface (CLI), also known as a terminal or command prompt. This is a text-based interface where you type commands to interact with your operating system.
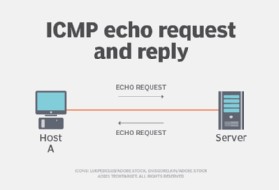
When you issue a ping command, your computer sends a small data packet to the specified target device. This packet is called an “ICMP Echo Request” – essentially, a message asking the target device to respond. If the target device is online and able to communicate, it sends back an “ICMP Echo Reply” packet. The ping utility then displays the results, showing you whether the target device responded, how long it took for the response to arrive, and other useful information.
3. The Anatomy of a Ping Request: Diving Deep into ICMP
The Internet Control Message Protocol (ICMP) is the workhorse behind the ping command. It’s a fundamental protocol used for diagnostic and error reporting in IP networks. ICMP operates at the network layer of the TCP/IP model, working alongside IP to ensure reliable communication.
Here’s how ICMP is used in a ping request:
- Echo Request: When you initiate a ping, your computer creates an ICMP Echo Request packet. This packet contains a header with information like the source and destination IP addresses, as well as a data payload.
- Transmission: The ICMP Echo Request packet is encapsulated within an IP packet and sent to the target device.
- Reception: The target device receives the IP packet and extracts the ICMP Echo Request.
- Echo Reply: If the target device is configured to respond to ping requests, it creates an ICMP Echo Reply packet. This packet is essentially a copy of the Echo Request, with the source and destination addresses reversed.
- Transmission (Reply): The ICMP Echo Reply packet is encapsulated within an IP packet and sent back to the originating computer.
- Reception (Reply): The originating computer receives the IP packet and extracts the ICMP Echo Reply.
- Results: The ping utility analyzes the Echo Reply and displays the results, including the round-trip time (RTT), packet loss, and other relevant information.
Understanding ICMP is crucial for comprehending how ping works and for troubleshooting network issues. ICMP is also used for other important network functions, such as:
- Destination Unreachable: Indicates that a destination is unreachable, either because the network is down or the target device is not online.
- Time Exceeded: Indicates that a packet has exceeded its time-to-live (TTL) and has been discarded by a router.
- Redirect: Instructs the sending device to use a different route to reach the destination.
4. Interpreting Ping Results: Decoding the Numbers
The output of a ping command provides valuable insights into the health and performance of your network connection. Here’s a breakdown of the key metrics:
- Round-Trip Time (RTT): This is the most important metric, representing the time it takes for a packet to travel from your computer to the target device and back. RTT is measured in milliseconds (ms). Lower RTT values indicate a faster and more responsive connection. High RTT values can indicate network congestion, routing issues, or a slow connection.
- Packet Loss: This indicates the percentage of packets that were sent but did not receive a response. Packet loss can be caused by network congestion, faulty hardware, or unreliable connections. Packet loss can significantly impact network performance, leading to slow loading times, dropped connections, and other issues.
- Time-to-Live (TTL): This value represents the maximum number of hops a packet can take before being discarded. Each time a packet passes through a router, the TTL value is decremented. If the TTL reaches zero, the packet is discarded to prevent routing loops. The TTL value can provide information about the network path the packet is taking.
- Bytes: This indicates the size of the data packet being sent. The default ping packet size is typically 32 bytes, but you can often adjust this value using command-line options.
- Destination Host Unreachable: This error message indicates that the target device is unreachable. This could be due to a network outage, a misconfigured IP address, or a firewall blocking the connection.
- Request Timed Out: This error message indicates that the ping request timed out before receiving a response. This can be caused by network congestion, a slow connection, or a firewall blocking the connection.
By analyzing these metrics, you can gain valuable insights into the performance of your network connection and identify potential problems.
5. Pinging in Action: Practical Examples and Scenarios
Let’s look at some practical examples of how to use the ping command in different scenarios:
-
Checking Internet Connectivity: To verify that you have a working internet connection, you can ping a well-known website like Google:
ping google.comIf the ping is successful and you receive replies, it indicates that your internet connection is working. If you receive “Destination Host Unreachable” or “Request Timed Out” errors, it suggests that there may be a problem with your internet connection.
 pinging google to check internet connectivity
pinging google to check internet connectivity -
Troubleshooting a Network Printer: If you’re having trouble connecting to a network printer, you can ping its IP address to check if it’s online:
ping 192.168.1.100Replace
192.168.1.100with the actual IP address of your printer. If the ping is successful, it indicates that the printer is online and reachable. If the ping fails, it suggests that there may be a problem with the printer’s network connection or that the printer is turned off. -
Diagnosing Network Latency: To measure the latency between your computer and a remote server, you can ping the server’s IP address and analyze the RTT values:
ping 8.8.8.88.8.8.8is the IP address of Google’s public DNS server. By pinging this server, you can get an estimate of the latency between your computer and the internet. High RTT values may indicate network congestion or a slow connection. -
Basic Network Troubleshooting: Pinging a device on your local network can help you quickly determine if the device is connected and responsive. If you can ping the device but still can’t access its services, the issue may be with the device’s software or configuration, rather than a network connectivity problem.
These are just a few examples of how you can use the ping command to troubleshoot network issues. With a little practice, you’ll be able to use ping to diagnose a wide range of network problems.
6. Advanced Ping Techniques: Beyond the Basics
While the basic ping command is useful, there are several advanced techniques that can provide more detailed information about your network connection.
-
Adjusting Packet Size: You can use the
-loption (on Windows) or the-soption (on Linux/macOS) to adjust the size of the ping packet. This can be useful for testing the maximum transmission unit (MTU) of your network.ping -l 1472 google.com (Windows) ping -s 1472 google.com (Linux/macOS)This command sends a ping packet with a data payload of 1472 bytes. If the ping is successful, it indicates that your network supports an MTU of at least 1500 bytes (1472 bytes of data + 28 bytes of IP and ICMP headers).
-
Setting the Time-to-Live (TTL): You can use the
-ioption (on Windows) or the-toption (on Linux/macOS) to set the TTL value of the ping packet. This can be useful for tracing the route that a packet takes to reach its destination.ping -i 1 google.com (Windows) ping -t 1 google.com (Linux/macOS)This command sends a ping packet with a TTL value of 1. This means that the packet will be discarded after passing through one router. By increasing the TTL value gradually, you can identify the routers along the path to the destination.
-
Continuous Ping: You can use the
-toption (on Windows) or the-foption (on Linux/macOS) to send ping requests continuously until you manually stop the command. This can be useful for monitoring network connectivity over time.ping -t google.com (Windows) ping -f google.com (Linux/macOS)To stop the continuous ping, press
Ctrl+C. -
Using Ping with Hostnames: You can ping a device using its hostname instead of its IP address. This is useful if you don’t know the IP address of the device, or if the IP address is dynamically assigned.
ping mycomputer.localThis command pings the device with the hostname
mycomputer.local.
By mastering these advanced ping techniques, you can gain a deeper understanding of your network connection and troubleshoot network issues more effectively.
7. Ping vs. Traceroute: Choosing the Right Tool
While ping is useful for checking reachability and measuring latency, it doesn’t provide information about the path that a packet takes to reach its destination. For that, you need a different tool called traceroute (or tracert on Windows).
Traceroute works by sending a series of ICMP or UDP packets with increasing TTL values. The first packet has a TTL of 1, the second has a TTL of 2, and so on. Each router along the path decrements the TTL value and forwards the packet. When the TTL reaches zero, the router sends an ICMP “Time Exceeded” message back to the originating computer. Traceroute uses these “Time Exceeded” messages to identify the routers along the path to the destination.
Here’s a comparison of ping and traceroute:
| Feature | Ping | Traceroute |
|---|---|---|
| Purpose | Check reachability, measure latency | Trace the path to a destination |
| Protocol | ICMP Echo Request/Reply | ICMP or UDP with varying TTL values |
| Output | RTT, packet loss | List of routers along the path, RTT for each hop |
| Use Cases | Basic connectivity testing, latency measurement | Identifying routing issues, mapping network topology |
When to use ping:
- You want to quickly check if a device is online and reachable.
- You want to measure the latency between your computer and a remote server.
- You want to troubleshoot basic network connectivity issues.
When to use traceroute:
- You want to identify the path that a packet takes to reach its destination.
- You want to diagnose routing problems or identify bottlenecks in the network.
- You want to map the network topology and understand how your network is connected.
Both ping and traceroute are valuable tools for network troubleshooting. By understanding their strengths and weaknesses, you can choose the right tool for the job.
8. Pinging and Network Security: Addressing the Risks
While ping is a valuable tool for network diagnostics, it can also be used for malicious purposes. One common security concern is “ping flooding,” a type of denial-of-service (DoS) attack where an attacker overwhelms a target device with a flood of ping requests, making it unavailable to legitimate users.
Here are some ways that ping can be used in network attacks:
- Ping Flood: As mentioned above, this involves sending a large number of ping requests to a target device, overwhelming its resources and causing it to become unresponsive.
- Ping of Death: This involves sending a ping packet that is larger than the maximum allowed size, causing the target device to crash. This vulnerability was more common in older operating systems but is still a potential risk in some cases.
- Smurf Attack: This involves sending ping requests to a broadcast address with the source address spoofed to be the target device. This causes all devices on the network to send replies to the target device, amplifying the attack.
To mitigate these risks, network administrators often implement security measures such as:
- Rate Limiting: Limiting the number of ping requests that can be sent to a device within a given time period.
- Firewall Rules: Blocking ICMP traffic or only allowing it from trusted sources.
- Intrusion Detection Systems (IDS): Monitoring network traffic for suspicious patterns, such as ping floods, and alerting administrators to potential attacks.
- Disabling ICMP: While disabling ICMP can prevent some types of attacks, it can also make it more difficult to troubleshoot network issues. Therefore, it’s important to carefully consider the trade-offs before disabling ICMP.
It’s important to be aware of the security risks associated with ping and to take appropriate measures to protect your network.
9. Pinging in Gaming: Minimizing Latency for a Smooth Experience
In online gaming, ping (often referred to as “latency”) is a critical factor that affects the responsiveness and smoothness of the gameplay. High ping values can result in noticeable lag, making it difficult to react quickly and accurately.
Here’s how ping affects online gaming:
- Lag: High ping causes a delay between your actions (e.g., pressing a button) and the corresponding reaction in the game. This can make it difficult to aim, move, and perform other actions effectively.
- Rubberbanding: This occurs when your character appears to move erratically, jumping back and forth between different positions. Rubberbanding is often caused by high ping and packet loss.
- Disconnects: In extreme cases, high ping and packet loss can lead to disconnects from the game server.
Ideally, gamers want to have the lowest possible ping to minimize lag and ensure a smooth gaming experience. Here are some factors that can affect ping in gaming:
- Distance to Server: The farther you are from the game server, the higher your ping will be.
- Internet Connection Speed: A slow internet connection can increase your ping.
- Network Congestion: Network congestion can cause delays and increase your ping.
- Router Configuration: A poorly configured router can increase your ping.
- Background Applications: Applications that consume bandwidth, such as streaming services or file downloads, can increase your ping.
Here are some tips for reducing ping in gaming:
- Choose a Server Closer to You: Select a game server that is located closer to your geographic location.
- Use a Wired Connection: A wired Ethernet connection is generally more stable and has lower latency than a wireless Wi-Fi connection.
- Close Background Applications: Close any applications that are consuming bandwidth in the background.
- Optimize Your Router: Make sure your router is properly configured and updated with the latest firmware.
- Use a Gaming VPN: A gaming VPN can help to reduce ping by routing your traffic through a faster and more direct path to the game server.
By optimizing your network connection and choosing the right game server, you can minimize ping and enjoy a smoother and more responsive gaming experience.
10. Troubleshooting Ping Issues: A Step-by-Step Guide
If you’re experiencing problems with ping, here’s a step-by-step guide to help you troubleshoot the issue:
- Check Your Internet Connection: Make sure your internet connection is working properly. You can do this by browsing the web or running a speed test.
- Ping Your Router: Ping your router’s IP address to check if you can communicate with your local network. If you can’t ping your router, there may be a problem with your network cable or router configuration.
- Ping a Public DNS Server: Ping a public DNS server, such as Google’s
8.8.8.8, to check if you can reach the internet. If you can ping the DNS server but can’t browse the web, there may be a problem with your DNS settings. - Check Your Firewall: Make sure your firewall is not blocking ICMP traffic. If you’re using a software firewall, check its settings to ensure that ping requests are allowed. If you’re using a hardware firewall, consult its documentation for instructions on how to configure ICMP filtering.
- Check Your Network Cables: Make sure your network cables are properly connected and not damaged. Try using a different network cable to see if that resolves the issue.
- Restart Your Router and Computer: Restarting your router and computer can often resolve temporary network issues.
- Contact Your Internet Service Provider (ISP): If you’ve tried all of the above steps and are still experiencing problems with ping, contact your ISP for assistance. There may be a problem with their network infrastructure.
By following these steps, you can systematically troubleshoot ping issues and identify the root cause of the problem.
11. Pinging on Different Operating Systems: Windows, macOS, and Linux
The ping command is available on all major operating systems, including Windows, macOS, and Linux. However, there may be slight differences in the syntax and options available on each platform.
Windows:
- To access the ping command on Windows, open the Command Prompt by searching for “cmd” in the Start menu.
- The basic syntax for the ping command on Windows is:
ping [hostname or IP address] - Some useful options on Windows include:
-t: Ping continuously until stopped manually.-n [count]: Send a specified number of ping requests.-l [size]: Set the size of the ping packet.-i [TTL]: Set the Time-to-Live (TTL) value.
macOS and Linux:
- To access the ping command on macOS and Linux, open the Terminal application.
- The basic syntax for the ping command on macOS and Linux is:
ping [hostname or IP address] - Some useful options on macOS and Linux include:
-c [count]: Send a specified number of ping requests.-s [size]: Set the size of the ping packet.-t [TTL]: Set the Time-to-Live (TTL) value.-f: Flood ping (send ping requests as fast as possible).
While the basic functionality of the ping command is the same on all operating systems, it’s important to be aware of the differences in syntax and options when troubleshooting network issues on different platforms.
12. The Future of Pinging: Evolving Network Diagnostics
While ping has been a staple of network diagnostics for decades, it’s important to consider how it might evolve in the future. As networks become more complex and sophisticated, new tools and techniques are emerging to provide more detailed and comprehensive network monitoring and troubleshooting capabilities.
Here are some potential future trends in network diagnostics:
- Advanced Network Monitoring Tools: These tools provide real-time visibility into network performance, allowing administrators to identify and resolve issues proactively. They often include features such as:
- Deep Packet Inspection (DPI): Analyzing the contents of network packets to identify applications, protocols, and potential security threats.
- Network Flow Analysis: Tracking the flow of traffic across the network to identify bottlenecks and anomalies.
- Artificial Intelligence (AI): Using AI algorithms to automatically detect and diagnose network problems.
- Cloud-Based Network Monitoring: Cloud-based network monitoring solutions offer several advantages, including scalability, flexibility, and ease of deployment. They allow administrators to monitor their networks from anywhere in the world, without having to install and maintain on-premises hardware and software.
- Software-Defined Networking (SDN): SDN allows for centralized control and management of network resources, making it easier to optimize network performance and troubleshoot issues. SDN controllers can collect and analyze network data in real-time, providing valuable insights into network behavior.
- Network Automation: Network automation tools can automate many of the tasks involved in network management, such as configuration, provisioning, and troubleshooting. This can help to reduce errors, improve efficiency, and free up network administrators to focus on more strategic initiatives.
While these advanced tools and techniques are becoming increasingly important, ping will likely remain a valuable tool for basic network diagnostics for the foreseeable future. Its simplicity and ubiquity make it a useful tool for quickly checking reachability and measuring latency.
13. Frequently Asked Questions (FAQs) About Pinging
Here are some frequently asked questions about pinging:
| Question | Answer |
|---|---|
| What is the difference between ping and traceroute? | Ping checks reachability and measures latency, while traceroute traces the path a packet takes to reach its destination. |
| What does “Request Timed Out” mean? | It means that the ping request did not receive a response within the allotted time. This can be caused by network congestion, a slow connection, or a firewall blocking the connection. |
| What is a good ping time? | A good ping time depends on the application. For online gaming, a ping time under 50ms is ideal. For general web browsing, a ping time under 100ms is acceptable. |
| Can ping be used for malicious purposes? | Yes, ping can be used for malicious purposes, such as ping flooding attacks. |
| How do I reduce my ping time? | Choose a server closer to you, use a wired connection, close background applications, optimize your router, and use a gaming VPN. |
| Is ping the same as latency? | Ping is a tool used to measure latency. Latency refers to the delay between sending a request and receiving a response. |
| What is ICMP? | ICMP stands for Internet Control Message Protocol. It’s a protocol used for diagnostic and error reporting in IP networks. |
| How do I ping a website? | Open the Command Prompt (Windows) or Terminal (macOS/Linux) and type ping [website address]. For example, ping google.com. |
| What does packet loss indicate? | Packet loss indicates that some of the ping requests did not reach the destination or the responses were not received. This can be caused by network congestion, faulty hardware, or unreliable connections. |
| Can I disable ping? | Yes, you can disable ping by blocking ICMP traffic on your firewall. However, this can make it more difficult to troubleshoot network issues. |
14. Conclusion: Mastering the Art of Pinging and Beyond
Pinging is a fundamental tool for network diagnostics, providing a quick and easy way to check reachability and measure latency. Whether you’re troubleshooting a home network, managing a corporate network, or simply trying to improve your online gaming experience, understanding ping is an essential skill.
By mastering the art of pinging and exploring the advanced techniques discussed in this guide, you can gain a deeper understanding of your network connection and troubleshoot network issues more effectively. And remember, if you have any questions or need further assistance, don’t hesitate to visit WHAT.EDU.VN and ask your questions for free. Our community of experts is always ready to help you navigate the complexities of the digital world.
Need Help? Ask Away at WHAT.EDU.VN!
Are you struggling to understand ping results? Do you have a specific network issue you’re trying to diagnose? Don’t hesitate to ask for help! At WHAT.EDU.VN, we provide a free platform for asking questions and getting answers from a community of experts.
- Stuck on a technical problem? Our knowledgeable users can provide step-by-step guidance.
- Confused about networking concepts? We’ll break them down into easy-to-understand terms.
- Need help choosing the right network tools? We can offer recommendations based on your specific needs.
Visit WHAT.EDU.VN today and ask your question for free!
Our mission is to make knowledge accessible to everyone. We believe that everyone should have the opportunity to learn and grow, regardless of their background or experience. That’s why we offer a free and open platform for asking questions and sharing knowledge.
Contact us:
- Address: 888 Question City Plaza, Seattle, WA 98101, United States
- WhatsApp: +1 (206) 555-7890
- Website: what.edu.vn
We look forward to helping you on your learning journey!
