WHAT.EDU.VN is here to clear up the confusion. Get ready to explore the world of Virtual LANs (VLANs), discovering how they segment networks for improved performance, security, and manageability. Dive in to unlock the benefits of network segmentation, virtual networks, and efficient network management today.
1. Understanding VLANs: The Basics
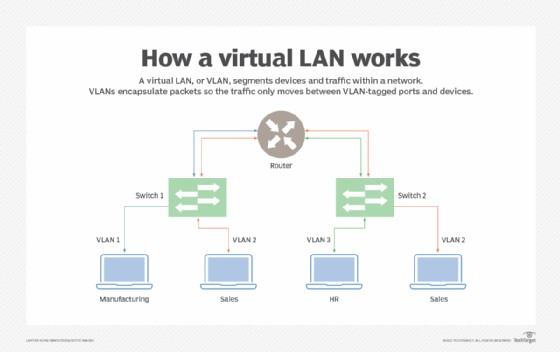
A Virtual LAN, or VLAN, is a logical grouping of network devices that behave as if they are connected to the same physical LAN, even though they may be scattered across different physical network segments. VLANs are created in software, allowing network administrators to segment their networks without the need for physical rewiring. This provides greater flexibility, security, and efficiency in network management.
1.1 What is the Definition of VLAN?
A VLAN is a broadcast domain that is partitioned and isolated in a computer network at the data link layer (OSI layer 2). VLANs are logical groupings of devices that function as if they are on their own independent network, regardless of their physical location.
1.2 What is the Purpose of VLANs?
VLANs serve several critical purposes in modern network environments:
- Segmentation: VLANs divide a physical network into multiple logical networks, isolating traffic and improving security.
- Security: VLANs allow administrators to control which devices can communicate with each other, reducing the risk of unauthorized access.
- Performance: By limiting the size of broadcast domains, VLANs reduce network congestion and improve overall performance.
- Management: VLANs simplify network administration by allowing administrators to group devices based on function, department, or other criteria.
1.3 How Does a VLAN Work?
VLANs operate at the data link layer (Layer 2) of the OSI model. When a device sends a frame, the switch examines the destination MAC address and forwards the frame only to ports that are members of the same VLAN. This ensures that traffic is isolated within the VLAN.
VLANs use a process called VLAN tagging to identify which VLAN a frame belongs to. When a frame enters a switch, the switch adds a VLAN tag to the frame’s header. This tag contains the VLAN ID, which identifies the VLAN to which the frame belongs. When the frame exits the switch, the tag is removed.
 VLAN Tagging
VLAN Tagging
2. Why Use VLANs? Exploring the Benefits
VLANs offer a wide range of benefits for organizations of all sizes. From improved security to simplified network management, VLANs can help you optimize your network infrastructure.
2.1 Enhanced Security
VLANs enhance network security by isolating traffic and limiting the scope of broadcast domains. This prevents unauthorized access to sensitive data and reduces the risk of network breaches.
- Traffic Isolation: VLANs prevent traffic from one VLAN from being seen by devices on another VLAN.
- Access Control: VLANs allow administrators to control which devices can communicate with each other.
- Reduced Attack Surface: By limiting the scope of broadcast domains, VLANs reduce the potential attack surface of the network.
2.2 Improved Network Performance
VLANs improve network performance by reducing network congestion and limiting the size of broadcast domains. This allows devices to communicate more efficiently and reduces the amount of unnecessary traffic on the network.
- Reduced Broadcast Traffic: VLANs limit the scope of broadcast domains, reducing the amount of broadcast traffic on the network.
- Improved Bandwidth Utilization: By reducing network congestion, VLANs improve bandwidth utilization.
- Faster Data Transfer: VLANs can improve data transfer speeds by reducing the amount of unnecessary traffic on the network.
2.3 Simplified Network Management
VLANs simplify network management by allowing administrators to group devices based on function, department, or other criteria. This makes it easier to configure, monitor, and troubleshoot the network.
- Logical Grouping: VLANs allow administrators to group devices based on logical criteria.
- Centralized Management: VLANs can be managed centrally, making it easier to configure and monitor the network.
- Simplified Troubleshooting: VLANs simplify troubleshooting by isolating network problems to specific VLANs.
2.4 Cost Savings
VLANs can help organizations save money by reducing the need for physical rewiring and hardware upgrades. By segmenting the network logically, VLANs allow organizations to make the most of their existing infrastructure.
- Reduced Cabling Costs: VLANs reduce the need for physical rewiring, saving on cabling costs.
- Delayed Hardware Upgrades: VLANs allow organizations to make the most of their existing hardware, delaying the need for upgrades.
- Lower Operational Costs: VLANs simplify network management, reducing operational costs.
3. Types of VLANs: Static vs. Dynamic
VLANs can be classified into two main types: static VLANs and dynamic VLANs. Each type has its own advantages and disadvantages, and the best choice for your network will depend on your specific needs and requirements.
3.1 Static VLANs
Static VLANs, also known as port-based VLANs, are configured manually by assigning switch ports to specific VLANs. This type of VLAN is simple to set up and manage, making it a good choice for small to medium-sized networks with relatively stable configurations.
- Manual Configuration: Static VLANs are configured manually by assigning switch ports to specific VLANs.
- Simple Management: Static VLANs are easy to set up and manage.
- Fixed Assignments: Port assignments are fixed and do not change automatically.
3.2 Dynamic VLANs
Dynamic VLANs automatically assign devices to VLANs based on criteria such as MAC address, IP address, or user authentication. This type of VLAN is more complex to set up but offers greater flexibility and scalability, making it a good choice for larger networks with more dynamic environments.
- Automatic Assignment: Dynamic VLANs automatically assign devices to VLANs based on predefined criteria.
- Increased Flexibility: Dynamic VLANs offer greater flexibility and scalability.
- Complex Configuration: Dynamic VLANs are more complex to set up and manage than static VLANs.
4. How to Configure VLANs: A Step-by-Step Guide
Configuring VLANs can seem daunting, but with a step-by-step guide, you can easily set up VLANs on your network. The following steps provide a general overview of the VLAN configuration process. Consult your switch documentation for specific instructions.
4.1 Planning Your VLAN Structure
Before you start configuring VLANs, it’s important to plan your VLAN structure. This involves identifying the different groups of devices that you want to isolate and assigning VLAN IDs to each group.
- Identify Device Groups: Determine the different groups of devices that need to be isolated.
- Assign VLAN IDs: Assign unique VLAN IDs to each group.
- Document Your Plan: Document your VLAN plan for future reference.
4.2 Creating VLANs on Your Switch
The next step is to create the VLANs on your switch. This typically involves using the switch’s command-line interface (CLI) or web-based management interface.
- Access the Switch: Access the switch’s CLI or web-based management interface.
- Create VLANs: Use the appropriate commands or interface to create the VLANs, specifying the VLAN IDs and names.
- Verify VLAN Creation: Verify that the VLANs have been created successfully.
4.3 Assigning Ports to VLANs
Once you have created the VLANs, you need to assign switch ports to the appropriate VLANs. This tells the switch which VLAN each port belongs to.
- Select Ports: Select the ports that you want to assign to a VLAN.
- Assign VLANs: Use the appropriate commands or interface to assign the ports to the VLANs.
- Verify Port Assignments: Verify that the ports have been assigned to the correct VLANs.
4.4 Configuring Trunk Ports
If you have multiple switches in your network, you will need to configure trunk ports to allow VLAN traffic to pass between switches. Trunk ports carry traffic for multiple VLANs.
- Select Trunk Ports: Select the ports that will be used as trunk ports.
- Configure Trunking: Use the appropriate commands or interface to configure trunking on the ports, specifying the allowed VLANs.
- Verify Trunk Configuration: Verify that trunking has been configured correctly.
4.5 Testing Your VLAN Configuration
After you have configured your VLANs, it’s important to test the configuration to ensure that everything is working correctly. This involves verifying that devices on different VLANs cannot communicate with each other and that devices on the same VLAN can communicate with each other.
- Test Connectivity: Test connectivity between devices on different VLANs.
- Test Isolation: Verify that devices on different VLANs cannot communicate with each other.
- Troubleshoot Issues: Troubleshoot any issues that you encounter.
5. VLAN Use Cases: Real-World Examples
VLANs are used in a variety of real-world scenarios to improve network security, performance, and manageability. Here are a few common VLAN use cases:
5.1 Separating Guest Networks
Many organizations provide guest Wi-Fi access to visitors. VLANs can be used to isolate the guest network from the internal network, preventing unauthorized access to sensitive data.
- Create a Guest VLAN: Create a separate VLAN for guest Wi-Fi access.
- Isolate Guest Traffic: Prevent guest traffic from accessing the internal network.
- Implement Security Policies: Implement security policies to protect the internal network from guest devices.
5.2 Isolating VoIP Traffic
Voice over IP (VoIP) traffic requires low latency and high bandwidth. VLANs can be used to prioritize VoIP traffic and ensure high-quality voice communication.
- Create a VoIP VLAN: Create a separate VLAN for VoIP traffic.
- Prioritize VoIP Traffic: Prioritize VoIP traffic over other types of traffic.
- Implement QoS Policies: Implement Quality of Service (QoS) policies to ensure high-quality voice communication.
5.3 Segmenting Departmental Networks
In large organizations, VLANs can be used to segment departmental networks, isolating traffic and improving security. This prevents unauthorized access to sensitive data and reduces the risk of network breaches.
- Create Departmental VLANs: Create separate VLANs for each department.
- Isolate Departmental Traffic: Prevent traffic from one department from accessing another department’s network.
- Implement Access Controls: Implement access controls to restrict access to sensitive data.
5.4 Securing IoT Devices
The Internet of Things (IoT) is rapidly expanding, and many IoT devices have weak security. VLANs can be used to isolate IoT devices from the main network, preventing them from being used as entry points for attacks.
- Create an IoT VLAN: Create a separate VLAN for IoT devices.
- Isolate IoT Traffic: Prevent IoT traffic from accessing the main network.
- Implement Security Policies: Implement security policies to protect the network from IoT devices.
6. VLAN Best Practices: Tips for Optimal Performance
To ensure that your VLANs are performing optimally, it’s important to follow these best practices:
6.1 Use a Consistent VLAN Naming Convention
Use a consistent VLAN naming convention to make it easier to identify and manage your VLANs.
- Descriptive Names: Use descriptive names that reflect the purpose of each VLAN.
- Consistent Format: Use a consistent format for all VLAN names.
- Document Your Convention: Document your naming convention for future reference.
6.2 Limit the Number of Devices per VLAN
Limiting the number of devices per VLAN can improve network performance by reducing the size of broadcast domains.
- Consider Network Size: Consider the size of your network when determining the number of devices per VLAN.
- Monitor Performance: Monitor network performance to identify VLANs that are becoming congested.
- Adjust as Needed: Adjust the number of devices per VLAN as needed to optimize performance.
6.3 Use VLAN Trunking Protocol (VTP) Wisely
VTP is a Cisco-proprietary protocol that simplifies VLAN management by allowing you to propagate VLAN configurations across multiple switches. However, VTP can also be a security risk if not configured properly.
- Secure Your VTP Configuration: Secure your VTP configuration with a password.
- Use VTP Pruning: Use VTP pruning to limit the propagation of VLAN information to only the switches that need it.
- Consider Alternative Solutions: Consider alternative VLAN management solutions if VTP is not appropriate for your network.
6.4 Regularly Review and Update Your VLAN Configuration
Regularly review and update your VLAN configuration to ensure that it is still meeting your needs.
- Assess Your Needs: Assess your network needs on a regular basis.
- Identify Inefficiencies: Identify any inefficiencies in your VLAN configuration.
- Update as Needed: Update your VLAN configuration as needed to optimize performance and security.
7. Common VLAN Misconceptions
There are several common misconceptions about VLANs that can lead to confusion and misconfiguration. Let’s debunk some of these myths to ensure a clear understanding.
7.1 VLANs are a Replacement for Firewalls
The Misconception: VLANs provide the same level of security as firewalls.
The Reality: VLANs provide network segmentation, which enhances security by isolating traffic. However, they do not offer the advanced threat protection, intrusion detection, and access control features of a firewall. Firewalls operate at a higher layer of the OSI model and provide comprehensive security measures that VLANs alone cannot offer. For robust security, use VLANs in conjunction with firewalls.
7.2 VLANs Always Improve Network Performance
The Misconception: Implementing VLANs automatically guarantees improved network performance.
The Reality: While VLANs can improve performance by reducing broadcast domains, improper configuration can lead to performance bottlenecks. Overly complex VLAN setups or misconfigured trunk links can create inefficiencies. Proper planning and configuration are essential to realizing the performance benefits of VLANs.
7.3 All Devices on the Same VLAN Can Communicate Freely
The Misconception: Devices on the same VLAN can always communicate with each other without any restrictions.
The Reality: By default, devices on the same VLAN can communicate freely. However, access control lists (ACLs) can be implemented within a VLAN to restrict communication between specific devices or subnets. This allows for more granular control over network traffic and enhances security.
7.4 VLANs Eliminate the Need for Physical Network Segmentation
The Misconception: VLANs make physical network segmentation entirely unnecessary.
The Reality: VLANs provide logical segmentation, which is highly flexible and cost-effective. However, in some high-security environments, physical segmentation may still be necessary to provide an additional layer of isolation. VLANs and physical segmentation can complement each other in a comprehensive security strategy.
7.5 VLANs are Only for Large Networks
The Misconception: VLANs are too complex and only beneficial for large, enterprise-level networks.
The Reality: VLANs can be beneficial for networks of all sizes. Even small networks can benefit from the enhanced security and improved organization that VLANs provide. Implementing VLANs in a small network can help isolate guest devices, separate VoIP traffic, or segment different departments.
8. Troubleshooting Common VLAN Issues
Even with careful planning and configuration, VLAN issues can arise. Here are some common problems and how to troubleshoot them.
8.1 Connectivity Problems Between VLANs
The Problem: Devices on different VLANs cannot communicate with each other.
Possible Causes:
- Missing or Misconfigured Router: Inter-VLAN routing is required for communication between VLANs. Ensure that a router is properly configured to route traffic between VLANs.
- Incorrect IP Addresses: Devices may have incorrect IP addresses or subnet masks. Verify that each device has an IP address within the correct subnet for its VLAN.
- Firewall Rules: Firewall rules may be blocking traffic between VLANs. Check the firewall configuration to ensure that traffic is allowed between the necessary VLANs.
Troubleshooting Steps:
- Verify Router Configuration: Check that the router is configured to route traffic between VLANs.
- Check IP Addresses: Ensure that devices have correct IP addresses and subnet masks.
- Examine Firewall Rules: Review firewall rules to identify any blocking rules.
8.2 Devices on the Same VLAN Cannot Communicate
The Problem: Devices on the same VLAN cannot communicate with each other.
Possible Causes:
- Incorrect VLAN Assignments: Devices may be assigned to the wrong VLAN. Verify that each device is connected to a port assigned to the correct VLAN.
- Port Configuration Issues: Port configuration issues, such as disabled ports or incorrect speed/duplex settings, can prevent communication.
- Spanning Tree Protocol (STP) Issues: STP can sometimes block ports to prevent loops, which can disrupt communication within a VLAN.
Troubleshooting Steps:
- Verify VLAN Assignments: Check that devices are connected to ports assigned to the correct VLAN.
- Examine Port Configuration: Ensure that ports are enabled and have correct speed/duplex settings.
- Check STP Status: Review STP status to identify any blocked ports.
8.3 Broadcast Traffic Spilling Over to Other VLANs
The Problem: Broadcast traffic from one VLAN is being seen by devices on other VLANs.
Possible Causes:
- Misconfigured Trunk Ports: Trunk ports may be allowing traffic from VLANs that should be isolated.
- VTP Configuration Issues: VTP may be incorrectly propagating VLAN information across the network.
- Routing Loops: Routing loops can cause broadcast traffic to be forwarded to unintended VLANs.
Troubleshooting Steps:
- Verify Trunk Port Configuration: Check that trunk ports are only allowing traffic from the intended VLANs.
- Examine VTP Configuration: Review VTP configuration to ensure that VLAN information is being propagated correctly.
- Check for Routing Loops: Identify and eliminate any routing loops in the network.
8.4 VLAN Performance Bottlenecks
The Problem: Network performance within a VLAN is slower than expected.
Possible Causes:
- Overloaded VLAN: The VLAN may be overloaded with too many devices, causing congestion.
- Insufficient Bandwidth: The VLAN may not have enough bandwidth to support the traffic load.
- QoS Configuration Issues: Quality of Service (QoS) may not be properly configured to prioritize critical traffic.
Troubleshooting Steps:
- Monitor VLAN Traffic: Monitor traffic within the VLAN to identify congestion.
- Increase Bandwidth: Increase bandwidth to the VLAN if necessary.
- Optimize QoS Configuration: Properly configure QoS to prioritize critical traffic.
9. The Future of VLANs: Trends and Innovations
As network technology evolves, so do VLANs. Here are some trends and innovations shaping the future of VLANs:
9.1 VXLAN (Virtual Extensible LAN)
VXLAN is an encapsulation protocol that extends VLANs beyond the traditional 4,096 VLAN ID limit. VXLAN uses a 24-bit VLAN ID, allowing for over 16 million VLANs. This is crucial in large-scale cloud environments where many tenants require isolated networks.
Key Benefits of VXLAN:
- Scalability: Supports a much larger number of VLANs compared to traditional VLANs.
- Flexibility: Enables the creation of virtual networks that span multiple physical networks.
- Encapsulation: Encapsulates Layer 2 frames within UDP packets for transport over Layer 3 networks.
9.2 Software-Defined Networking (SDN) and VLANs
SDN centralizes network control, allowing for more dynamic and automated VLAN management. SDN controllers can programmatically configure VLANs across the network, simplifying network administration and improving agility.
Key Benefits of SDN with VLANs:
- Centralized Control: Simplifies VLAN management through a central controller.
- Automation: Automates VLAN configuration and provisioning.
- Flexibility: Enables dynamic VLAN creation and modification based on network needs.
9.3 Network Virtualization Overlays (NVOs)
NVOs use encapsulation techniques, such as VXLAN, to create virtual networks on top of existing physical networks. This allows for greater flexibility and scalability in network design.
Key Benefits of NVOs:
- Abstraction: Abstracts the underlying physical network, allowing for more flexible network design.
- Scalability: Supports a large number of virtual networks.
- Isolation: Provides isolation between virtual networks.
9.4 Intent-Based Networking (IBN) and VLANs
IBN allows network administrators to define the desired state of the network, and the network automatically configures itself to meet those requirements. This simplifies VLAN management by automating the configuration process.
Key Benefits of IBN with VLANs:
- Simplified Management: Simplifies VLAN management by automating the configuration process.
- Improved Agility: Enables faster network changes and deployments.
- Reduced Errors: Reduces the risk of manual configuration errors.
10. Need Expert Advice?
Navigating the complexities of VLANs can be challenging. Whether you’re planning a new network, troubleshooting existing issues, or exploring advanced technologies like VXLAN and SDN, WHAT.EDU.VN is here to help.
Do you have questions about VLANs?
- Unsure where to start with VLAN configuration?
- Experiencing performance issues with your current VLAN setup?
- Need guidance on integrating VLANs with other network technologies?
Don’t hesitate to reach out to us!
At WHAT.EDU.VN, we understand the challenges of modern network management. That’s why we offer a free consultation service to answer all your questions and provide expert guidance tailored to your specific needs.
Here’s how we can help:
- Answer Your Questions: Get clear, concise answers to your VLAN questions from our team of network experts.
- Provide Expert Guidance: Receive personalized recommendations and best practices for your network environment.
- Offer Practical Solutions: Discover actionable steps to improve your network performance, security, and manageability.
Contact us today for a free consultation!
- Address: 888 Question City Plaza, Seattle, WA 98101, United States
- WhatsApp: +1 (206) 555-7890
- Website: WHAT.EDU.VN
Let what.edu.vn be your trusted partner in network excellence.
Remember, optimizing your network with VLANs is just the beginning. We’re here to support you every step of the way. Don’t wait—reach out to us now and take your network to the next level.
